In today’s security-conscious environment, the importance of optimizing key control through effective key inventory management strategies cannot be overstated. By meticulously evaluating current procedures and embracing digital solutions, organizations can greatly enhance operational efficiency and security. However, the implementation of such strategies involves careful consideration of various factors, including the integration of technology, formulation of stringent access policies, and the commitment to ongoing audits and training. This opens up a broader discussion on the balance between technological advancement and human oversight in the domain of key management. How do organizations navigate these complexities to guarantee robust security and accountability?
To navigate the complexities of key inventory management effectively, organizations must leverage both innovative technologies and best practices. Understanding the pivotal role of key inventory management software in boosting security protocols is essential. By streamlining key inventory management processes, businesses can achieve a balance between technological efficiencies and the necessary human oversight. This approach not only enhances operational effectiveness but also fortifies overall security measures, thereby ensuring accountability and compliance with regulatory standards. Embracing such integrated strategies is the cornerstone of modern key management systems.
Summary:
- Implement a digital tracking system to enhance real-time visibility and control over keys.
- Establish clear access policies to define who can use specific keys and how.
- Conduct regular audits and reconciliations to identify and address discrepancies promptly.
- Develop training and awareness programs to educate staff on key management protocols.
- Evaluate existing key management procedures to pinpoint inefficiencies and security vulnerabilities.
Assessing Current Key Management
To effectively enhance inventory management, it is crucial to conduct a thorough assessment of the current key management system. This initial step involves evaluating existing procedures, identifying weaknesses, and pinpointing inefficiencies that could lead to potential security breaches or operational bottlenecks. The assessment should encompass a detailed review of how keys are issued, tracked, returned, and stored. Additionally, it is essential to scrutinize the accountability mechanisms in place for key holders and the protocols for dealing with lost or unreturned keys.
Understanding the flow and usage of keys within an organization provides valuable insights into the demand patterns and critical control points that require fortification. This analysis should also extend to the physical and administrative layers of key management, examining the durability and security of key storage solutions, as well as the effectiveness of record-keeping practices. Gathering this information lays the groundwork for identifying areas ripe for improvement and sets the stage for developing a more streamlined and secure key inventory management strategy. This structured approach ensures that any subsequent enhancements are data-driven and targeted, thereby maximizing the impact on overall operational efficiency and security.
Implementing a Digital Tracking System
Implementing a digital tracking system marks a pivotal advancement in streamlining key inventory management by offering real-time visibility and control over key movements. This technological solution transforms traditional key management processes, enabling organizations to monitor and manage their key inventory with unprecedented efficiency. By adopting digital tracking, entities can greatly reduce the risk of lost or unaccounted keys, thereby enhancing security and reducing potential vulnerabilities.
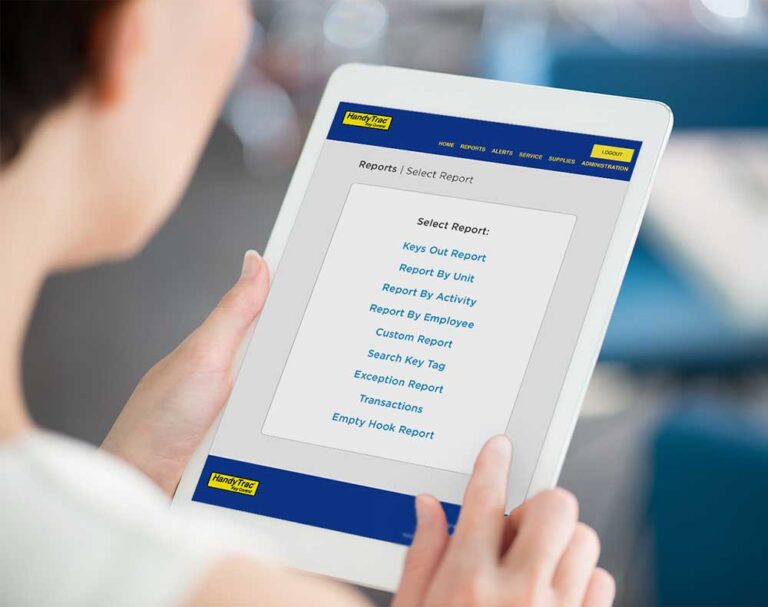
Digital tracking systems employ a variety of technologies, including RFID tags, barcode scanners, and cloud-based software, to create a detailed overview of key allocations and movements within an organization. This allows for immediate updates and alerts, ensuring that all key transactions are accurately recorded and accessible. The system’s capability to provide detailed reports on key usage patterns and history is invaluable for auditing and compliance purposes, offering insights that facilitate better decision-making and policy development.
Moreover, the shift to a digital platform streamlines the process of issuing and returning keys, minimizing manual errors and saving considerable time. With features such as automated reminders for key returns and instant deactivation of lost keys, organizations can maintain a higher level of security and operational efficiency. Implementing a digital tracking system is therefore a critical step towards modernizing key inventory management and securing assets.
Establishing Clear Access Policies
Following the integration of a digital tracking system, establishing clear access policies forms the next vital step in enhancing the security and efficiency of key inventory management. These policies serve as the foundation for determining who has access to certain keys, under what circumstances they can be accessed, and how this access is monitored and managed over time. It’s about setting boundaries and making sure that every key’s usage aligns with the organization’s security protocols and business needs.
| Policy Component | Description | Purpose |
| Access Rights | Defines who is authorized to access specific keys. | Ensures keys are only used by those with a legitimate need. |
| Usage Guidelines | Outlines the acceptable use cases for each key. | Prevents misuse and enhances accountability. |
| Monitoring & Reporting | Details the methods for tracking key usage and reporting anomalies. | Facilitates oversight and swift response to irregularities. |
Regular Audits and Reconciliations
Conducting regular audits and reconciliations is essential for maintaining the integrity and accuracy of key inventory management systems. This process involves systematically reviewing and verifying the actual inventory of keys against the records maintained within the management system. By doing so, organizations can identify discrepancies early, such as missing keys or unauthorized duplications, and take prompt corrective actions. These audits not only enhance security by ensuring that only authorized individuals have access to certain areas but also contribute to the efficient management of resources.
Implementing a structured schedule for audits and reconciliations is pivotal. Depending on the size and complexity of the organization, these checks can be conducted monthly, quarterly, or annually. Utilizing automated key management systems can significantly streamline this process, allowing for real-time tracking and reporting of key statuses. This technology reduces the likelihood of human error and provides a robust audit trail for compliance purposes.
Furthermore, it is important to involve a cross-functional team in the audit process. This ensures that all aspects of key management, from issuance to return or disposal, are scrutinized, reinforcing the system’s reliability and effectiveness. Regular audits and reconciliations, thus, play a critical role in optimizing key control and safeguarding organizational assets.
Training and Awareness Programs
Effective training and awareness programs are essential components of a strong key inventory management strategy. These initiatives guarantee that all personnel involved in key control understand their roles and responsibilities, reducing the risk of security breaches and unauthorized access. By focusing on educating employees about the importance of key management, organizations can foster a culture of security consciousness that permeates every level of the operation.
Training programs should cover the proper handling and storage of keys, the process for checking keys in and out, and the steps to take in the event of a lost or stolen key. Additionally, they must emphasize the significance of adhering to established protocols and the potential consequences of non-compliance. Awareness efforts can be reinforced through regular communication, including updates on policy changes, reminders about key security principles, and feedback on the program’s effectiveness.
To maximize their impact, training and awareness programs should be tailored to the specific needs of the organization and include practical, hands-on sessions where possible. Regular assessments can help identify areas for improvement and ensure that the training remains relevant and effective. Ultimately, well-designed training and awareness programs are vital to maintaining the integrity of a key inventory management system.
Discover More About Us – HandyTrac
HandyTrac: Pioneering Multifamily Solutions for Over Two Decades
For more than 20 years, the innovators behind HandyTrac have been at the forefront of developing unique programs and services tailored for the multifamily industry. Their journey of innovation includes the creation of the “Little Buddy” rent roll program, Clever Computer Internet Services, and pioneering online key control and work order systems. HandyTrac stands as a beacon of progress in the multifamily space, continuously evolving to meet and exceed the needs of property owners and managers.
Revolutionizing Key Control with Biometrics
HandyTrac has achieved a significant milestone by introducing the first integrated biometric identity verification system tailored specifically for key control. This groundbreaking development not only enhances security but also incorporates modern conveniences such as WiFi capabilities, bilingual options, and comprehensive online key activity reporting. The integration of these features demonstrates HandyTrac’s dedication to providing cutting-edge solutions that optimize operations and security for multifamily properties.
The Low-Cost Leader in Key Control
HandyTrac proudly positions itself as the “Low-Cost Leader” in key control, emphasizing its commitment to affordability without compromising quality or innovation. This philosophy has resonated with over 800 companies, making HandyTrac key control systems a trusted choice among leading names in the industry such as Abbey Residential, Greystar, Irvine Company, and many more.
Core Values That Drive Success
HandyTrac’s success is rooted in its unwavering dedication to core values that guide every aspect of its operations:
- Frugality: A relentless emphasis on cost control and efficiency ensures that HandyTrac can offer the lowest prices without sacrificing quality.
- Integrity: HandyTrac’s commitment to keeping promises, both to customers and within the team, fosters trust and reliability.
- Reliability: Products designed for durability, with systems installed over 15 years ago still in operation today, attest to the reliability that HandyTrac offers.
- Service: Acclaimed for exceptional service, HandyTrac prides itself on meeting and exceeding customer expectations.
- Technical Innovation: With 3 U.S. patents and another pending, HandyTrac’s focus on customer-driven innovation remains unwavering, as they continue to invent and refine solutions that address the evolving needs of the multifamily industry.
As HandyTrac moves forward, its history of innovation, commitment to quality, and focus on serving the multifamily sector cements its role as a key player in shaping the future of property management solutions.
→ Discover more about us:
–FAQ
Our Products:

Description:
Introducing the HandyTrac Standard Touch: Elevating Security and Convenience
In the realm of property management and security, the HandyTrac Standard Touch system is a game-changer. Designed with user-friendliness and efficiency at its core, this innovative system is revolutionizing how we manage access and maintain security. Let’s delve into the standout features that make the Standard Touch a must-have for any modern facility.
A Closer Look at the HandyTrac Standard Touch Features
- Expansive 7″ Touchscreen Interface – Navigate effortlessly through the system’s features with a generous 7-inch touchscreen display. Its intuitive design ensures that managing access is both quick and straightforward.
- Dual Access Modes – Offering flexibility, the system accommodates both badge and PIN entry, ensuring authorized staff can access it with ease.
- Seamless Wi-Fi Connectivity – Built-in Wi-Fi means you’re always connected, allowing for real-time updates and access from anywhere.
- Bilingual Accessibility – With options for both English and Spanish speakers, the system is designed to be inclusive, ensuring a wider range of users can operate it comfortably.
- Efficient Key Management – The one-touch building pull feature streamlines the process of pulling multiple keys, enhancing efficiency.
- Centralized Reporting for Multi-Property Management – Manage reports for multiple properties with a single login, making overview and analysis more straightforward than ever.
- Reliable Audit Trails – With reports backed up to Amazon Web Services, you have a dependable audit trail that ensures information is both secure and retrievable.
- Customizable Codes – Tailor your activity codes to suit your specific needs, adding a layer of personalization and control.
- Instantaneous Reporting – Gain immediate insights with reports on key allocations, including who has which key, the purpose, and when it was returned.
- Streamlined Work Order Review – Review individual work orders with a single touch, enhancing efficiency and response times.
- Flexible Cabinet Options – Whether you need a single or double cabinet setup, the system offers flexibility to accommodate your specific spatial and operational requirements.

Description:
Introducing HandyTrac Touch: Elevate Your Security with Advanced Biometric Solutions
In a world where security and convenience are paramount, HandyTrac Touch emerges as a top-tier solution, ingeniously blending cutting-edge biometric technology with a user-friendly large touchscreen display. This all-in-one unit is designed to offer unmatched security, comprehensive reporting, and unparalleled flexibility for property management.
Key Features of HandyTrac Touch:
- Intuitive 7″ Touch Screen: Navigate with ease through the system’s features on a large, responsive touchscreen display.
- Secure Biometric Access: Enhance security with fingerprint access, ensuring only authorized personnel can operate the system.
- Seamless Connectivity: With a built-in Wi-Fi connection, stay connected and manage your properties efficiently.
- Language Versatility: Cater to a diverse workforce with bilingual options, accommodating both English and Spanish speakers.
- Effortless Key Management: Simplify the process of managing multiple keys with one-touch building pull integration.
- Unified Management: Conveniently review reports for multiple properties with a single login, streamlining property oversight.
- Dependable Audit Trail: Benefit from secure, cloud-backed reports via Amazon Web Services, guaranteeing data integrity and availability.
- Tailored Activity Codes: Customize your system with activity codes that match your operation’s needs.
- Immediate Reporting: Gain instant insights into key transactions, including details on who has the key, the reason, and return timings.
- Simplified Work Order Review: Access individual work orders with ease, enhancing maintenance coordination and execution.
- Enhanced Door Alarm: Boost security with a built-in door alarm feature that provides immediate SMS Text and email notifications upon unauthorized access.
- Detailed Unit Notes: Maintain important information for each unit, from occupancy details to specific alerts like late sleepers or pets.
- Key Access Restrictions: Ensure controlled access by restricting certain employees from accessing keys to specific units.
- Seamless Yardi Integration: For Yardi users, unlock a tailored experience with service order and staff data importation, allowing for efficient staff overview and direct execution of work orders via the Touch datalog.
HandyTrac Touch represents a leap forward in property management technology, combining the latest in biometric security with the convenience of modern connectivity and reporting functionalities. Whether you’re overseeing multiple properties or focused on enhancing your current security protocols, HandyTrac Touch offers a robust solution to meet and surpass your requirements. Discover a new standard of property management with HandyTrac Touch, where advanced technology meets operational excellence.

Description:
The Platinum HandyTrac Systems feature a suite of advanced capabilities designed to enhance security, efficiency, and user experience in key management. These systems are equipped with a comprehensive array of features, including:
- A spacious 10-inch touchscreen interface that enhances user interaction and visibility, capable of displaying 50% more units simultaneously for expedited key handling.
- A powerful 8-core ARM Cortex-X1 processor running at 1.8GHz, ensuring swift operation and responsiveness.
- Direct access to full website functionalities from the device’s display, making system management seamless and integrated.*
- An installation-friendly design that facilitates easy mounting on walls.
- Connectivity options include both Wi-Fi and Ethernet, ensuring flexible and reliable data transfer.
- Support for multiple languages including English, Spanish, and Tagalog, catering to diverse user groups.
- A comprehensive warranty covering the entire system, alongside USA-based technical support for timely assistance.
- Options for either single or double cabinet configurations, accommodating different operational scales.
- State-of-the-art biometric fingerprint access for enhanced security measures.
- A significant capacity enhancement, offering a 50% increase in the display of units, streamlining the key request process.
- Integration of One Touch Building Pull feature for efficient management of multiple key withdrawals.
- A robust audit trail supported by backups to Amazon Web Services, ensuring data integrity and compliance.
- Customizable activity codes and instant reports on key transactions, including key withdrawals, user identification, and return timings.
- A built-in door alarm system complemented by email notification for unauthorized access alerts.
- Features for adding notes and restrictions to specific units for tailored access control.
- Compatibility with Yardi systems, offering Yardi users a customizable experience through a secure work order system directly from the Touch interface. This includes importing service orders and staff data for streamlined operations.
*Note: Full website access feature is subject to future firmware updates.
Platinum Touch Overview: The Platinum Touch system integrates biometric security features with a large touchscreen interface, encapsulating the apex of security and operational flexibility. This system allows management teams authorized access to manage the system directly on the device, leveraging the large display for enhanced visibility and efficiency in key management tasks.
Click here to learn more:
Last Word
In conclusion, managing key inventory effectively is critical for optimal operational efficiency and security in today’s digital era. To achieve this, organizations need to review their existing key management systems, implement digital tracking systems, establish clear access policies, and adopt regular audits and staff training. These strategies will help simplify the complex realm of key management and ensure robust organization-wide security.
One of the standout solutions in this landscape emerges from HandyTrac, a pioneer in multifamily solutions and key control. With a steadfast commitment to technologically advanced, cost-effective, and reliable key management systems like the Standard Touch and the Premium Touch, HandyTrac is fundamentally transforming key inventory strategies. It merges practical features with modern conveniences and security measures, providing a comprehensive solution that can adapt to the unique needs of various organizations.